Network Online Course
Lesson 2 - Communication Standards
B. OSI Reference Model
OSI Reference Model
- International Standards Organization
- Open Systems Interconnect Reference Model
- 7 layer model of networking
- Each layer only communicates to one above and below
- Very slow to be implemented
OSI Reference Model
For a greater understanding of data communications and networking, the Open Systems Interconnect (OSI) seven layer reference model of networking is usually used. The model was designed by the International Standards Organization (ISO) in order to clarify the relationship of various network components to each other.The purpose of the model
The OSI model is a model of how communications might work. It was designed by the International Standards Organization with input from many other organizations including standards committees, manufacturers and governments. The model includes all of the functions necessary for communications and divides them by functionality into seven divisions or layers. The purpose of this model include the following- to provide general design guidelines for data communication systems.
- to divide the communication process into well-defined, functional areas (called layers), facilitating the creation of network products and encouraging the interchangeability of network components.
- to promote the goal of communications between different types of systems by encouraging the development of internetworking devices.
- to make sure that all functions needed for communications are addressed and that none are left out.
- to avoid duplication of functions thereby increasing efficiency.
- to design independence for each layer from other layers. This facilitates the interoperability of products from different manufacturers and insures that the end-user can substitute one vendor’s product for another.
- to produce a learning tool that can be used to understand how communications in modern computer systems works.
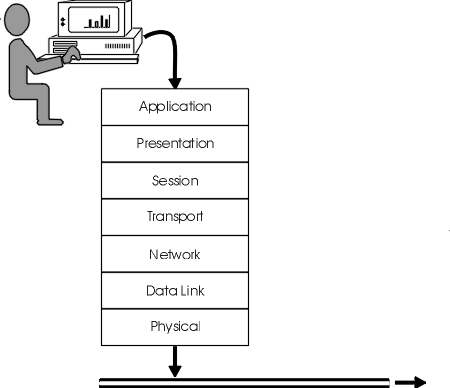
Figure 14: The OSI Reference model of communications
Some basic rules
The OSI model has some basic rules. They include- a layer may only communicate with the layer above and below and may not circumvent these layers.
- a layer must be independent of any other layer.
What the layers do
The following is a discussion of each layer. Figure 14 illustrates the seven layers in their correct order.Application layer
The application layer is responsible for providing network services to users and their applications. It is not, however, the user’s application or the operating system, such as Windows.- It provides a user interface — a good example is the type of terminal emulation a host requires, such as VT100 or 3270.
- It provides network services such as file transfer, mail service or terminal emulation e.g. FTP, Telnet, SNMP.
Presentation layer
The presentation layer deals with syntax and grammatical rules for presenting data to the application layer (not the user). This includes encoding, decoding and otherwise converting data. It is responsible for the following.- Character sets — the code used to represent characters e.g. the ASCII of personal computers vs. EBCDIC, used by IBM mainframes. A gateway has to convert character sets when a PC communicates with an IBM mainframe.
- Compression and decompression of data — some communication protocols include compression of data. Kermit is one such protocol.
- Encrypts and decrypts data — moving data over a network safe from prying eyes is the job of encryption. There are many methods available for this including DES, RSA and SSL and public/private key schemes.
- Bit order translation — numbers are sent over the network as binary numbers. The meaning of the numbers is different if the computer starts with the leading bit first or the trailing bit. One is the most significant bit (MSB), the other is the least significant bit (LSB).
- Byte order translation — just as a byte is made up of bits, a message is made up of bytes. Should the most important byte be transmitted first or the least important? Intel microprocessors transmit the least significant first (called little Endian) while Motorola CPUs (Macintosh) transmit the most important first (called big Endian). Communication between PCs and Macintoshes must take this into account.
- File structure — another difference between PCs and Macintoshes is their file structure. Macintosh files are comprised of two files, called forks: the resource fork and the data fork. PC files are single entities .
| Character Sets | ||
| ASCII Created by ANSI |
7 bits | Used by PCs |
| ANSI | 8 bits | All Windows |
| Unicode Controlled by Uniforum |
16 bits | Windows NT/2000/2003/XP |
| Shift-JIS Japanese Industrial Standards Committee |
8 bits | Japanese character set Katakana |
| ISO-8859 Latin 1 | 8 bits | Used in HTML |
| EBCDIC IBM |
8 bits | Used by IBM mainframes |
Session layer
A session is an agreement to communicate between two entities and the session layer controls the setup, termination and other mechanics of this conversation.- It establishes and maintains connection e.g. intent to transmit, was it successful?
- It deals with name recognition (computer name, user name) and login.
- It deals with synchronization of data transmission by placing checkpoints within data stream so that if interrupted, the transmission can take up where it left off.
- It deals with upper layer errors in the communications process including problems with memory, storage space, printing.
- It handles remote procedure calls (RPCs), e.g. running a program on a remote computer.
Transport layer
The transport layer provides extra connection services including error correction.- It controls data flow, e.g. slows down transmission if buffers about to overflow.
- It fragments and reassembles data.
- It acknowledges successful transmission.
- It correct faulty transmission.
Network layer
The network layer is primarily responsible for getting information to the correct computer on the correct network.- It moves information to the correct address.
- It assembles and disassembles packets.
- It determines addressing and routing.
- It determines the best path.
Data Link layer
The data link layer creates the entity (the packet or frame) which is put onto the transmission media.- It controls access to the communications channel.
- It controls the flow of data.
- It organize data into logical frames.
- It identifies specific computers on the network.
- It detects errors.
Physical layer
The physical layer is not the transmission media (cable) itself, but is responsible for the specifications for the media and the electrical signal that goes on it.- It provides electrical and physical interface to the network.
- It specifies type of medium.
- It specifies how signals are transmitted.
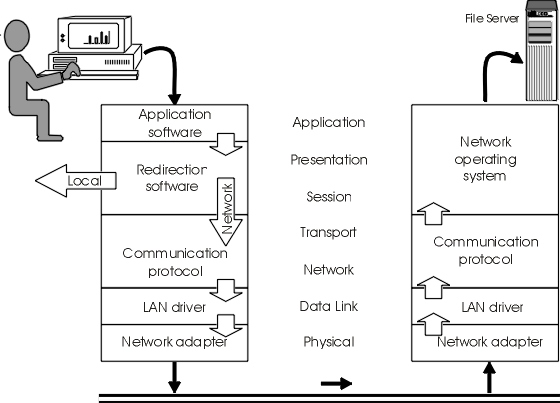
Figure 15: Data flow through the OSI model
Making a request
The process of moving data through the OSI model is illustrated above. It shows a request coming from a user at a workstation to a file server. The data, for example, the request to open a Word file, starts from the user. In fact, it starts with the Word program itself. It is passed to each layer where it is acted upon until it finally emerges as a packet on the network cable. It is received by the network interface card of the destination machine and then is passed through successive layers until it emerges at the top and is passed to the program running there.Notice two things about this process. There may not be a distinct piece of software for each of these layers. The functions of several layers may be combined into a single program. Secondly, layers may be missing entirely if their functions are not needed. OSI is just a model which is useful for learning about data communications and one which developers should try to design for. It does not necessarily represent the real world.
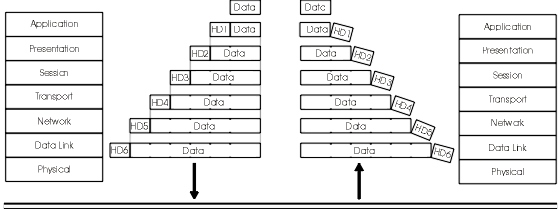
Figure 16: Encapsulation
Encapsulation
The process of moving data through successive layers is called encapsulation. Each layer takes the frame from the layer above. This becomes the new data or “payload”. It then adds information fields to the front of the data and possibly, an error correcting field to the back and then passes it on to the layer below where the complete frame becomes the new data. Because beginning and ending fields frame the data, this process is often called “framing”. Because the data is cradled within or enclosed inside, the process is also called “encapsulation”.At the receiving end, the process is reversed. At each layer, the framing fields for that layer are stripped off. Error correcting information, if any, is calculated. Then the data is passed up to the next layer and the process is repeated.
Although the process is cumbersome with a great deal of housekeeping involved, performance can still be excellent because it operates at electronic speeds. Improving the speed of communications is a priority for all those involved in this process, including the developers, vendors and administrators of the systems. An important element of fine tuning, however, is understanding the process as outlined above.Exercise 2-1: OSI Model Quiz
Exercise a: Label the layers of the OSI modelExercise b: Match the OSI layer with the function it provides
_________ Mediate access to communications channel; Organize data into frames
_________ Data representation (ASCII); Data compression and encryption
_________ Establish and maintain connections; Deal with upper layer errors
_________ Ensure reliability of delivered packets; Data flow and transmission errors
_________ Specifications for physical channel; Carry signals for all higher layers
_________ User interface; User applications
_________ Network addressing and routing; Packet assembly and disassembly
[Top of page][On to next section]